There are many topics about the internet, for example, privacy, security, and the ethical impacts of computing innovations. Privacy and security are very important to all users of internet, regardless of age, internet usage, and location. These are big concerns because of the risks of data collection and storage.

When you use the internet, you are "exchanging" or "communicating" data. Your personal information is being stored Sometimes, services collects you data and they might share and sell your data. There are many ways for hackers to steal data. Data can be easily taken and stolen if they are not protected properly.
This can be risky because it might cause data loss and data leak. Organizations should handle user data with good ethics and respect. They should also make sure the data is secure. Poor security of data can result in vulnerabilities and allow to data to be in the hand of unauthorized hackers and be used to do crime or bad things.
There are many misuses of computing resources. Like when unethical hackers get access to your data, they can use it to do a variety of things. They can steal your identity, money, and other personal information. They can also use your data to commit fraud and blackmail. More wrong uses of computing resources are illegal software distribution, denial of service attacks, cyber sabotage, cyber ransom, and much more.
Illegal software distribution is when someone distributes software without the permission of the owner. This is a crime because it is stealing. Denial of service attacks is when someone tries to make a website or service unavailable to users. This is a crime because it is disrupting the service. Cyber sabotage is when someone tries to damage or destroy data. This is a crime because it is destroying property. Cyber ransom is when someone tries to extort money from someone by threatening to release their data. This is a crime because it is extortion.

These are serious crime that anyone should watch out for. There are ways to protect yourself from these threats. You can implement firewall and intrusion detection systems, improve security firmware, encryption, and most importantly, test for security vulnerabilities by doing things like penetration tests. When using the internet, always make sure you are safe from these attacks and crimes
9 Types Of Computer MisuseMost internet crimes are basically unauthorized access to information that is being use in malicious ways. There are multiple ways to access data and information illegitimately. Common methods are, exploiting software vulnerabilities, exploiting insecure network, phishing, malware, spyware, exploiting passwords, and scams.
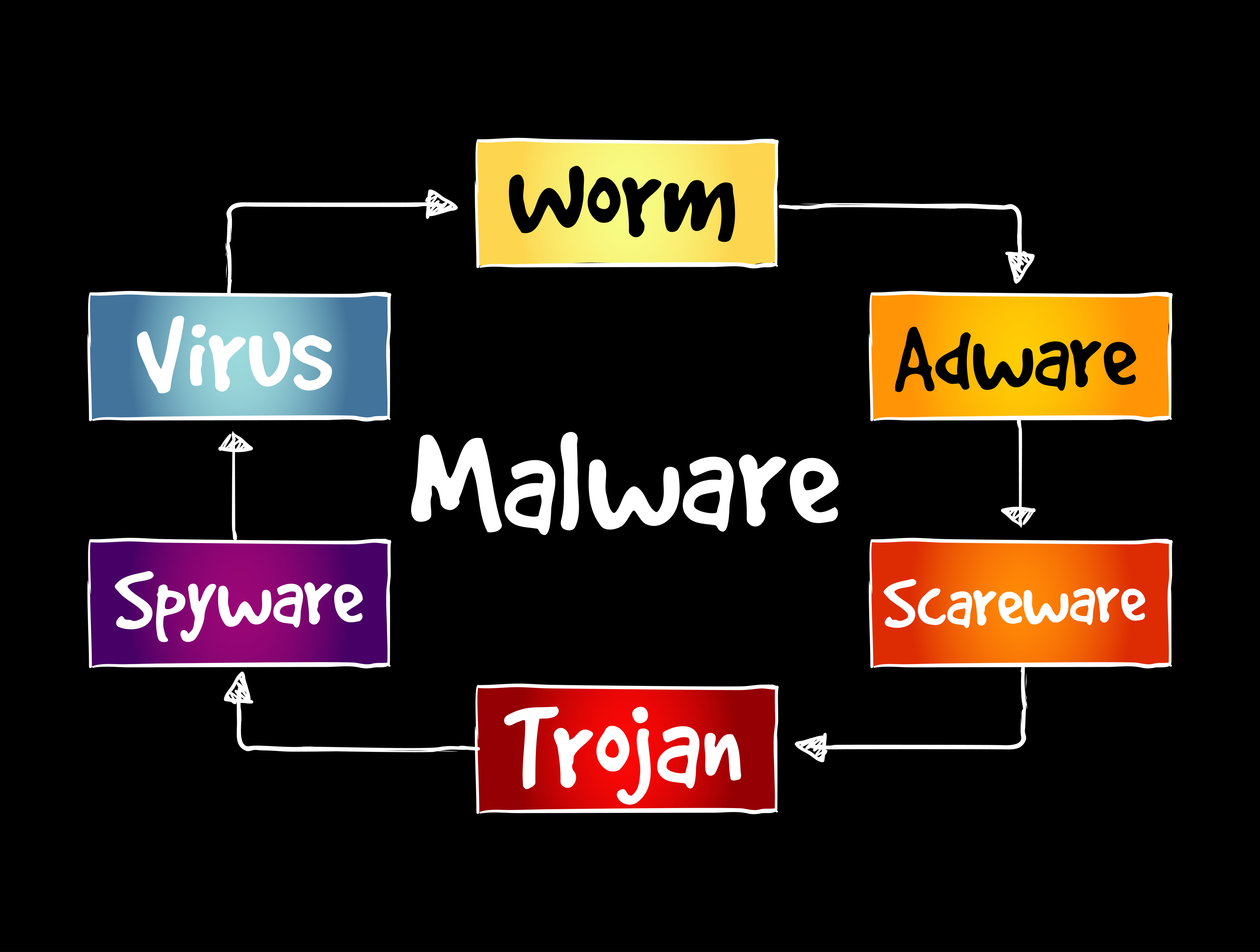
Exploiting software vulnerabilities is basically finding bugs in software, and use that to get access to data. exploiting insecure network is common in public wifi, because many of public wifi doesn't have good security measures, therefore, it is easy to exploit and find vulnerabilities. Phishing is when someone tries to trick you on the internet by pretending to be something that they are not. Malware are software that are specifically designed to get access to computers' system and it can be used to damage it or steal data. Spyware is another type of software that is made to infiltrate systems, they are use to spy on people and possibly get information or data.
To protect yourself from these threats, you need to be aware of them. Understanding what they are is beneficial and helpful for you to protect yourself. For the large majority of people to stop being victims of these threats, they need to be educated about them. And learn how to not fal for them.
Unauthorized AccessInnovation has huge benefits, but at the same time, some innovations are used by unethical hackers to benefit themselves and harm others. It can be a challenge to prevent dangerous innovation and solve problems. Computing innovations can be used to improve the quality of life, increase productivity, and make life easier. However, they can also be used to harm people.

For example, the internet has made it easier to communicate with people all over the world. It has also made it easier to access information and share it with others. However, it has also made it easier for hackers to steal data and commit crimes. The internet has also made it easier for people to spread false information and propaganda. This can be harmful to society. Then internet also made it easier for people to do bad things they wouldn't do in real life.

Although there are risks, in most cases, the benefits of computing innovation outweighs the risks and challenges of technology. It is important to be aware of the risks and challenges of technology. Best way to approach computing innovations and technology is to take advantage of the benefits and avoid or minimize the risks and challenges.
Advantages and Disadvantages of Technology